Fake email invoices: The expensive click
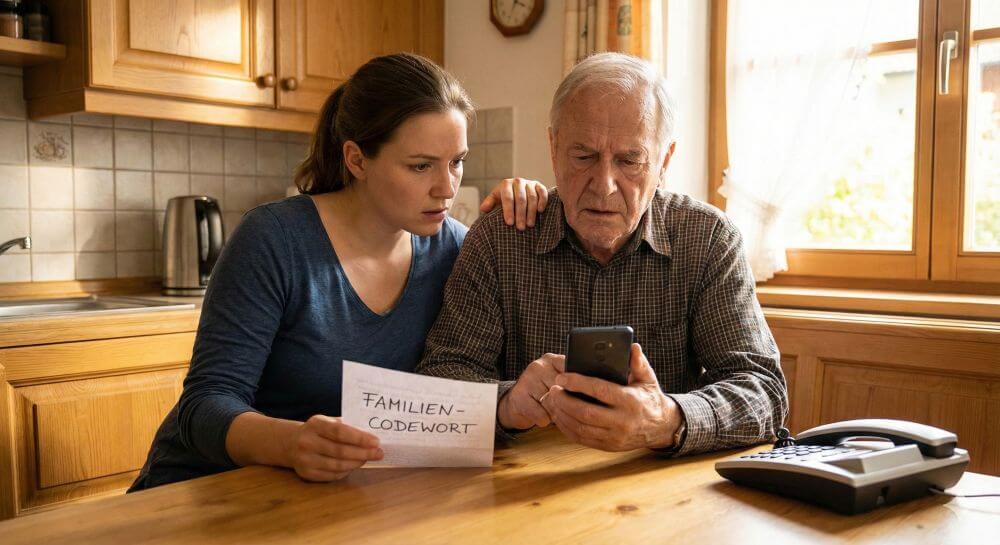
In the digital world, scams are commonplace and one of the most common scams is fake invoices sent via email. If a customer falls for such an email and pays the requested amount, it can be complicated and often impossible to get the money back. Scammers are becoming more sophisticated and the legal hurdles are high. This article sheds light on the legal aspects, gives tips on how to protect yourself and shows why the responsibility often lies with the customer himself. At a time when online transactions are becoming more common, understanding these issues is more important than ever.

Fake email invoices: The expensive click
In the digital world, scams are commonplace and one of the most common scams is fake invoices sent via email. If a customer falls for such an email and pays the requested amount, it can be complicated and often impossible to get the money back. Scammers are becoming more sophisticated and the legal hurdles are high. This article sheds light on the legal aspects, gives tips on how to protect yourself and shows why the responsibility often lies with the customer himself. At a time when online transactions are becoming more common, understanding these issues is more important than ever.

The scam with the fake invoice
The scam with the fake invoice
Fake invoices via email are a growing problem. Scammers often use official-looking logos and wording to trick their victims. The invoices may be for products or services that were never ordered or delivered.
How to recognize fake emails?
1. Unknown Sender
If the email comes from an unknown or suspicious address, one should be careful. Scammers often use similar but slightly different email addresses that appear legitimate at first glance.
2. Spelling and grammatical errors
Many fake emails contain spelling and grammatical errors. Professional companies usually pay attention to correct language.
3. Unusual salutation
If the email begins with a generic or unusual salutation, such as “Dear Customer” instead of your name, this could be an indication of a spoofed email.
4. Request for personal information
Phishing emails often ask for personal or financial information to be disclosed. Legitimate companies typically do not ask for such sensitive information via email.
5. Urgency
A common tactic used by scammers is to feign urgency, such as threatening fines or banning accounts if immediate action is not taken.
6. Unusual links or attachments
Suspicious links or attachments, especially if not expected, should be a red flag. Hover your mouse over the link (without clicking) to see the actual URL. Supposed invoices that are sent as an HTML document instead of the usual PDF document are also popular. If you receive an email with such an attachment, you can delete the email immediately. Because here you will also be directed to a fake website.
7. Unusual requests
If the email asks you to do something unusual, like pay an unfamiliar bill or click an unfamiliar link, be skeptical.
8. Check the company
If you are unsure whether an email is legitimate, contact the company directly using the official website or phone number, not the contact information provided in the suspicious email.
Fake invoices via email are a growing problem. Scammers often use official-looking logos and wording to trick their victims. The invoices may be for products or services that were never ordered or delivered.
How to recognize fake emails?
1. Unknown Sender
If the email comes from an unknown or suspicious address, one should be careful. Scammers often use similar but slightly different email addresses that appear legitimate at first glance.
2. Spelling and grammatical errors
Many fake emails contain spelling and grammatical errors. Professional companies usually pay attention to correct language.
3. Unusual salutation
If the email begins with a generic or unusual salutation, such as “Dear Customer” instead of your name, this could be an indication of a spoofed email.
4. Request for personal information
Phishing emails often ask for personal or financial information to be disclosed. Legitimate companies typically do not ask for such sensitive information via email.
5. Urgency
A common tactic used by scammers is to feign urgency, such as threatening fines or banning accounts if immediate action is not taken.
6. Unusual links or attachments
Suspicious links or attachments, especially if not expected, should be a red flag. Hover your mouse over the link (without clicking) to see the actual URL. Supposed invoices that are sent as an HTML document instead of the usual PDF document are also popular. If you receive an email with such an attachment, you can delete the email immediately. Because here you will also be directed to a fake website.
7. Unusual requests
If the email asks you to do something unusual, like pay an unfamiliar bill or click an unfamiliar link, be skeptical.
8. Check the company
If you are unsure whether an email is legitimate, contact the company directly using the official website or phone number, not the contact information provided in the suspicious email.
Legal Aspects
Legal Aspects
When a customer falls for a fake bill and pays, the responsibility often lies with them. Banks are usually not required to return the money because the transaction was authorized by the customer. However, there are some legal options that need to be checked on a case-by-case basis.
1. Prosecution of Fraudsters
Prosecuting perpetrators can be difficult, especially when they are based abroad. However, it is important to report the scam to the police as it can increase the chances of catching the perpetrators and bringing them to justice.
2. Consumer Protection
Some jurisdictions have consumer protection laws that could protect the consumer in certain circumstances. However, the exact rights and obligations may vary from country to country and from case to case.
3. Civil Claims
It might be possible to bring civil claims against the bank or company concerned if it can be shown that they acted negligently. However, this could be a lengthy and expensive process.
4. Privacy
If personal information was compromised through the scam, data protection laws could be relevant. Companies that do not adequately protect their customer data could be legally prosecuted.
5. Insurance Coverage
Some insurance policies may offer protection against fraud. It is worth checking your own insurance conditions and, if necessary, speaking to the insurer.
6. Legal advice
Since the legal situation is complex and depends on many factors, it is advisable to consult a lawyer in the event of fraud. A professional can assess the specific situation and indicate the best way to assert rights.
However, I warn against getting too much hope for success with the legal possibilities. Because it is not uncommon for the scammers to be based somewhere abroad and are hardly vulnerable to EU or even German law. Even tracking down the actual location of the company can become a detective work that customers then give up in exasperation.
The most important means and the best protection against fake invoices and fake shops on the Internet is and remains prevention, so that it doesn’t get that far in the first place. Take the time to check everything carefully in advance and use payment service providers with buyer protection such as PayPal.
When a customer falls for a fake bill and pays, the responsibility often lies with them. Banks are usually not required to return the money because the transaction was authorized by the customer. However, there are some legal options that need to be checked on a case-by-case basis.
1. Prosecution of Fraudsters
Prosecuting perpetrators can be difficult, especially when they are based abroad. However, it is important to report the scam to the police as it can increase the chances of catching the perpetrators and bringing them to justice.
2. Consumer Protection
Some jurisdictions have consumer protection laws that could protect the consumer in certain circumstances. However, the exact rights and obligations may vary from country to country and from case to case.
3. Civil Claims
It might be possible to bring civil claims against the bank or company concerned if it can be shown that they acted negligently. However, this could be a lengthy and expensive process.
4. Privacy
If personal information was compromised through the scam, data protection laws could be relevant. Companies that do not adequately protect their customer data could be legally prosecuted.
5. Insurance Coverage
Some insurance policies may offer protection against fraud. It is worth checking your own insurance conditions and, if necessary, speaking to the insurer.
6. Legal advice
Since the legal situation is complex and depends on many factors, it is advisable to consult a lawyer in the event of fraud. A professional can assess the specific situation and indicate the best way to assert rights.
However, I warn against getting too much hope for success with the legal possibilities. Because it is not uncommon for the scammers to be based somewhere abroad and are hardly vulnerable to EU or even German law. Even tracking down the actual location of the company can become a detective work that customers then give up in exasperation.
The most important means and the best protection against fake invoices and fake shops on the Internet is and remains prevention, so that it doesn’t get that far in the first place. Take the time to check everything carefully in advance and use payment service providers with buyer protection such as PayPal.
Popular Posts
The best AI text recognition tools compared
KI-Texte von ChatGPT und Co. sind allgegenwärtig. Doch wie unterscheiden Sie Mensch von Maschine? Wir vergleichen die Top-Tools wie Originality.ai und GPTZero. Erfahren Sie, welcher Detektor am genauesten ist und wo die technischen Grenzen der KI-Erkennung liegen.
Schatten-KI: Die undichte Stelle im Browser
Nutzen Ihre Mitarbeiter heimlich ChatGPT? Schatten-KI ist das unsichtbare Risiko für Ihre Datensicherheit. Sensible Infos landen oft auf fremden Servern. Lesen Sie, warum reine Verbote scheitern und wie Sie mit smarten Richtlinien Ihre Daten schützen, ohne Innovation zu bremsen.
Meta in court: Will the subscription requirement now be overturned?
Those who want an ad-free Facebook experience have to pay – or agree to extensive tracking. A lawsuit challenging this model is now underway. Will the mandatory subscription model be overturned in court? Find out why consumer advocates consider the practice illegal and what this means for users.
Cybersicherheit: Die 3 größten Fehler, die 90% aller Mitarbeiter machen
Hacker brauchen keine Codes, sie brauchen nur einen unaufmerksamen Mitarbeiter. Von Passwort-Recycling bis zum gefährlichen Klick: Wir zeigen die drei häufigsten Fehler im Büroalltag und geben praktische Tipps, wie Sie zur menschlichen Firewall werden.
Here’s how to protect your content from AI training.
AI models often train on your content without your permission. But you're not powerless. This article shows you effective strategies – from technical opt-outs and "poison pills" for image AI to closed paywalls – to regain control over your intellectual property.
How we all turned Google into our monopolist
Google's monopoly is homegrown – created by us. We chose the superior search engine, "free" services like Gmail and Maps, and ignored the competition. In exchange for convenience, we gave away our data and created the monopolist ourselves.
Popular Posts
The best AI text recognition tools compared
KI-Texte von ChatGPT und Co. sind allgegenwärtig. Doch wie unterscheiden Sie Mensch von Maschine? Wir vergleichen die Top-Tools wie Originality.ai und GPTZero. Erfahren Sie, welcher Detektor am genauesten ist und wo die technischen Grenzen der KI-Erkennung liegen.
Schatten-KI: Die undichte Stelle im Browser
Nutzen Ihre Mitarbeiter heimlich ChatGPT? Schatten-KI ist das unsichtbare Risiko für Ihre Datensicherheit. Sensible Infos landen oft auf fremden Servern. Lesen Sie, warum reine Verbote scheitern und wie Sie mit smarten Richtlinien Ihre Daten schützen, ohne Innovation zu bremsen.
Meta in court: Will the subscription requirement now be overturned?
Those who want an ad-free Facebook experience have to pay – or agree to extensive tracking. A lawsuit challenging this model is now underway. Will the mandatory subscription model be overturned in court? Find out why consumer advocates consider the practice illegal and what this means for users.
Cybersicherheit: Die 3 größten Fehler, die 90% aller Mitarbeiter machen
Hacker brauchen keine Codes, sie brauchen nur einen unaufmerksamen Mitarbeiter. Von Passwort-Recycling bis zum gefährlichen Klick: Wir zeigen die drei häufigsten Fehler im Büroalltag und geben praktische Tipps, wie Sie zur menschlichen Firewall werden.
Here’s how to protect your content from AI training.
AI models often train on your content without your permission. But you're not powerless. This article shows you effective strategies – from technical opt-outs and "poison pills" for image AI to closed paywalls – to regain control over your intellectual property.
How we all turned Google into our monopolist
Google's monopoly is homegrown – created by us. We chose the superior search engine, "free" services like Gmail and Maps, and ignored the competition. In exchange for convenience, we gave away our data and created the monopolist ourselves.