The business of your inbox:
Who buys and sells email addresses, and what they cost.
In the digital economy, data is the hardest currency, and the email address is often the master key to our digital identity. It’s not just a means of communication, but also the login name for almost all services, from online banking to social media. But behind the scenes, a lively marketplace exists—sometimes legal, sometimes illegal—where these addresses are traded like commodities.

The sources: Where does the data come from?
Before email addresses can be traded, they must be collected. The methods range from technically sophisticated to downright criminal.
A. The Illegal Route: Data Breaches and Hacking
This is the “dark” source. When large companies are hacked (as happened in the past with Yahoo, LinkedIn, and Marriott), millions of records end up on the dark web.
- The Sellers: Hacker collectives or individuals looking to make a quick buck.
- The Merchandise: Often not just the email address, but also associated passwords (in plain text or encrypted), phone numbers, and addresses.
B. The Gray Area: Harvesting and Scraping
This involves using automated bots that search the open internet for the “@” symbol.
- Web Scraping: Bots extract email addresses from websites, forums, legal notices, and social networks.
- Dictionary Attacks: Software generates millions of possible address combinations (e.g., firstname.lastname@gmail.com) and checks which of them exist.
C. The “Legal” Way: Co-Registration and Data Brokers
Many users voluntarily provide their data, often without realizing it.
- Sweepstakes & Free E-books: Those who participate often agree in the fine print to the transfer of their data to “partner companies.”
- Address Publishers & List Brokers: These companies legally collect data (often B2B data from commercial registers or through telephone surveys) and officially rent or sell these lists for marketing purposes.
The marketplaces: Where does trading take place?
Trading takes place on two completely different levels.
The Dark Web Marketplace
Specialized forums and marketplaces exist on the dark web for illegal data obtained through hacking. Transactions are usually conducted anonymously using cryptocurrencies (Bitcoin, Monero). Hierarchies and rating systems (similar to eBay) foster “trust” among criminals.
The Official Data Trade (Clearnet)
List brokers operate openly on the regular internet. They offer highly specialized lists, often for B2B (business-to-business) purposes.
Note regarding GDPR: In the EU, the purchase and use of email lists for B2C (business-to-consumer) advertising without explicit consent is extremely restrictive and usually illegal. B2B advertising is permitted in some cases under strict conditions, but even here, the market has been significantly impacted by the GDPR.
The buyers: Who pays for addresses?
Buyers’ motivations often determine the quality they require and the price they are willing to pay.
Spammers & Scammers (Affiliate Spam, Phishing): They prioritize quantity over quality. Their goal is to send millions of emails, hoping that a fraction of recipients will click on a fraudulent link.
Unscrupulous Marketers: Companies that want to make quick sales and don’t care about reputational damage or legal consequences.
Legitimate Sales Teams (mostly B2B): Companies looking for new business clients. They often purchase expensive, high-quality lists of decision-makers in a specific industry (e.g., “All IT managers in the mechanical engineering sector in Southern Germany”).
Recruiters: Headhunters buy lists of skilled professionals to contact them directly for jobs.
The price: How much does an email address cost?
The price of an email address varies wildly and depends almost entirely on its quality and the depth of data it contains. A bare email address is practically worthless; an email address linked to purchase intent is invaluable.
Factors that determine the price:
- Relevance: Was the address verified within the last month, or is the list five years old?
- Data depth (enrichment): Is only the email address known, or also name, age, gender, location, income, and interests?
- Exclusivity: Has the list been sold thousands of times, or is it “fresh”?
- B2B vs. B2C: Business contacts are almost always more expensive than personal contacts.
Rough price examples (estimated values):
| Type of data | Description | Estimated price |
|---|---|---|
| Bulk / Raw Lists (Mass) | Millions of unverified addresses, often old or from hacks. | $0.0001 – $0.01 per address (often as terabyte packages on the dark web for a few dollars) |
| Simple B2C leads | Consumer data with basic information (name, age). | $0.05 – $0.50 per record |
| Qualified B2C leads | Consumers with known purchase intentions (e.g., “Interested in private health insurance”). | $2,00 – $50,00+ per record |
| Targeted B2B contacts | Verified email from a specific decision-maker (e.g., CEO of a medium-sized company). | $0,50 – $5,00+per record |
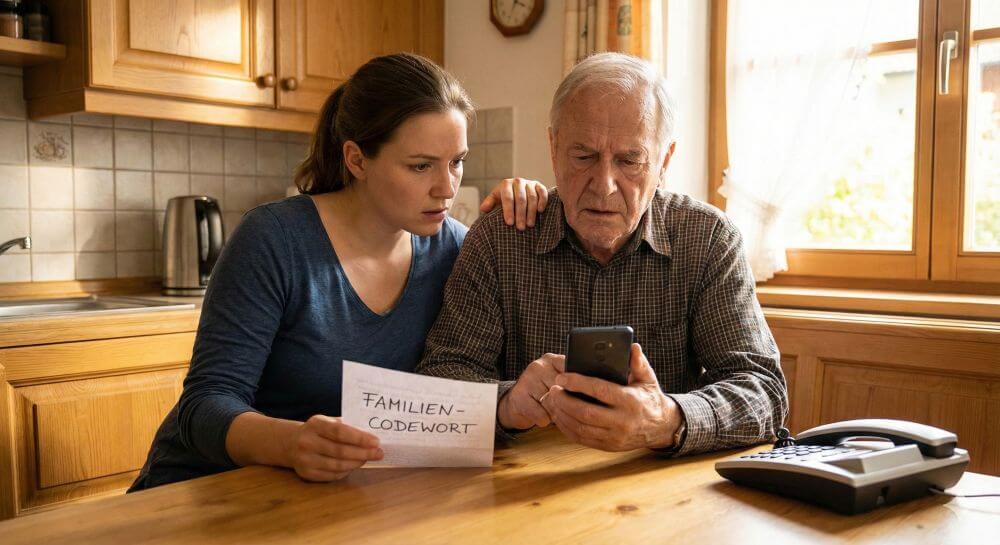
How can you protect yourself from that?
One must be realistic: 100% protection is virtually impossible if you actively participate in digital life. The goal is to minimize risk and control who has your data.
1. The “Two-Account Strategy” (Basic Protection)
Strictly separate your digital identities.
- The “Vault” address: Only for banks, government agencies, your closest friends, and important contracts. Never use this address for newsletters, contests, or unimportant forums.
- The “Spam” address: A second account with a free provider (GMX, Web.de, Gmail, etc.). Use this for everything else: online shopping, newsletter subscriptions, and free downloads. If this address receives too much spam, you can simply delete it and create a new one.
2. The “+” Trick (Alias Tracking)
Many email providers (including Gmail and Outlook) support so-called “sub-addressing.”
- How it works: If your address is max.muster@gmail.com, you can sign up for a service with max.muster+newsletter@gmail.com or max.muster+schuhshop@gmail.com. The email will still arrive in your regular inbox.
- The advantage: If you suddenly receive spam at max.muster+schuhshop@gmail.com, you know exactly that this specific online shop has shared your data or has been hacked.
3. “Throwaway” Addresses (For One-Time Use)
If you only need to quickly click a confirmation link to download a PDF or read an article, use temporary mailboxes.
- Services: Sites like 10 Minute Mail, Guerrilla Mail, or TrashMail generate a random address that self-destructs after a short time.
- Advantage: Your real address never appears anywhere.
4. Modern Alias Services (Premium Protection)
Large providers now integrate automatic protection features that are often better than the “+” trick because they are not easy for third parties to guess.
- Apple “Hide Email Address”: If you use iCloud+, Apple can create a unique random address for each website (e.g., df395xk@icloud.com) that forwards emails to you. If an address starts to get on your nerves, deactivate that one.
- Firefox Relay: A similar service from Mozilla that hides real addresses behind aliases.
5. Remain invisible to bots (obfuscation)
- Never publish your email address in plain text on websites, in forum signatures, or on public social media profiles. Bots scan the internet for it 24/7.
- If necessary: Use paraphrases like “max.muster [at] anbieter [dot] de” or use images that show your email address (bots have more difficulty reading text in images).
6. Data minimization & Use GDPR
- Remove the checkmark: When registering, pay meticulous attention to pre-selected checkboxes such as “Yes, I would like to receive partner offers.”
- Right to be forgotten: If you no longer use a service, don’t just unsubscribe from the newsletter. Exercise your right under the GDPR and request that the provider delete your entire account and all associated data.
Quick check: Has my data already been traded?
There’s a very well-known and reputable website run by a security researcher where you can check if your email address has already appeared in known data breaches (hacks):
Enter your email address there. If it has been “pwned” (compromised), the site will show you which service the data breach occurred at and what data (often including passwords!) was stolen.
Conclusion: A risky trade.
While trading email addresses is a purely high-volume business for criminals, legitimate companies are navigating a minefield. The European General Data Protection Regulation (GDPR) has introduced fines in the millions, making the simple purchase of lists too economically risky for many companies. The trend is therefore shifting away from buying third-party data towards the laborious but secure process of building one’s own legitimate email distribution lists.
Beliebte Beiträge
Warum dein Excel-Kurs Zeitverschwendung ist – was du wirklich lernen solltest!
Hand aufs Herz: Wann hast du zuletzt eine komplexe Excel-Formel ohne Googeln getippt? Eben. KI schreibt heute den Code für dich. Erfahre, warum klassische Excel-Trainings veraltet sind und welche 3 modernen Skills deinen Marktwert im Büro jetzt massiv steigern.
Microsoft Loop in Teams: The revolution of your notes?
What exactly are these Loop components in Microsoft Teams? We'll show you how these "living mini-documents" can accelerate your teamwork. From dynamic agendas to shared, real-time checklists – discover practical use cases for your everyday work.
Career booster 2026: These Microsoft Office skills will take you further!
A new year, new career opportunities! But which Office skills will really be in demand in 2026? "Skilled use" is no longer enough. We'll show you today's must-haves – like advanced Excel, using AI in the office, and relevant certifications for your resume.
Excel Tutorial: How to quickly and safely remove duplicates
Duplicate entries in your Excel lists? This distorts your data. Our tutorial shows you, using a practical example, how to clean up your data in seconds with the "Remove Duplicates" function – whether you want to delete identical rows or just values in a column.
Dynamic ranges in Excel: OFFSET function
The OFFSET function in Excel creates a flexible reference. Instead of fixing =SUM(B5:B7), the function finds the range itself, e.g., for the "last 3 months". Ideal for dynamic charts or dashboards that grow automatically.
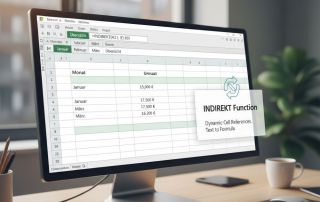
Mastering the INDIRECT function in Excel
The INDIRECT function in Excel converts text into a real reference. Instead of manually typing =January!E10, use =INDIRECT(A2 & "!E10"), where A2 contains 'January'. This allows you to easily create dynamic summaries for multiple worksheets.