The most important tips for online banking
The number of participants in online banking is growing, and is enjoying increasing enthusiasm.
In the year 2018, 50% of Germans now have online access to their checking account. Nevertheless, on closer examination, the proportion has grown by only about 5% in the past 5 years. The reasons for this are among others, often the recurrent reports about security vulnerabilities, or stolen records. Of course, this does not necessarily create trust among customers.
In part, however, it is also the case that the users even by ignorance, or negligence, your data in the hands of scammers, or at least make it easy. In our article, we would like to point out the most important points from our point of view, so that you can do your money conveniently and, above all, safely from home.
The most important tips for online banking
The number of participants in online banking is growing, and is enjoying increasing enthusiasm.
In the year 2018, 50% of Germans now have online access to their checking account. Nevertheless, on closer examination, the proportion has grown by only about 5% in the past 5 years. The reasons for this are among others, often the recurrent reports about security vulnerabilities, or stolen records. Of course, this does not necessarily create trust among customers.
In part, however, it is also the case that the users even by ignorance, or negligence, your data in the hands of scammers, or at least make it easy. In our article, we would like to point out the most important points from our point of view, so that you can do your money conveniently and, above all, safely from home.
1. Overview of the TAN procedure
1. Overview of the TAN procedure
After many attempts by the banks, the following procedures have now been established:
Although there are other methods, but basically it is as you have already noticed, always about as safe as possible to create a TAN or transfer.
After many attempts by the banks, the following procedures have now been established:
Although there are other methods, but basically it is as you have already noticed, always about as safe as possible to create a TAN or transfer.
2. Browser security in online banking
2. Browser security in online banking
Regardless of which of the above methods you use, they all presuppose that the entire chain of the components involved is protected.
And that includes the security of the PC and the browser used.
Note:
A good alternative to the standard browsers especially for online banking, but also for transactions via PayPal and other financial service providers offers the premium anti-virus software Bitdefender
This browser is specially secured by the attached anti-virus software to a high degree, and is absolutely recommendable from personal experience.
Regardless of which of the above methods you use, they all presuppose that the entire chain of the components involved is protected.
And that includes the security of the PC and the browser used.
Note:
A good alternative to the standard browsers especially for online banking, but also for transactions via PayPal and other financial service providers offers the premium anti-virus software Bitdefender
This browser is specially secured by the attached anti-virus software to a high degree, and is absolutely recommendable from personal experience.
3. Password security for online banking
3. Password security for online banking
Of course, all technical safety measures are useless if it fails the easiest. Namely the secure password.
Here we recommend that you think up a whole sentence that you may associate with personal events. And you should then change this as far as the e.g. every 2nd letter is capitalized, or the letter E is replaced by a 3.
You could then use special characters such as / or% between the words.
Basically, the more complex a password is, the better.
If you do not want to think of anything, you can also create an Online Password Generator. But it is better that you think your own.
Of course, all technical safety measures are useless if it fails the easiest. Namely the secure password.
Here we recommend that you think up a whole sentence that you may associate with personal events. And you should then change this as far as the e.g. every 2nd letter is capitalized, or the letter E is replaced by a 3.
You could then use special characters such as / or% between the words.
Basically, the more complex a password is, the better.
If you do not want to think of anything, you can also create an Online Password Generator. But it is better that you think your own.
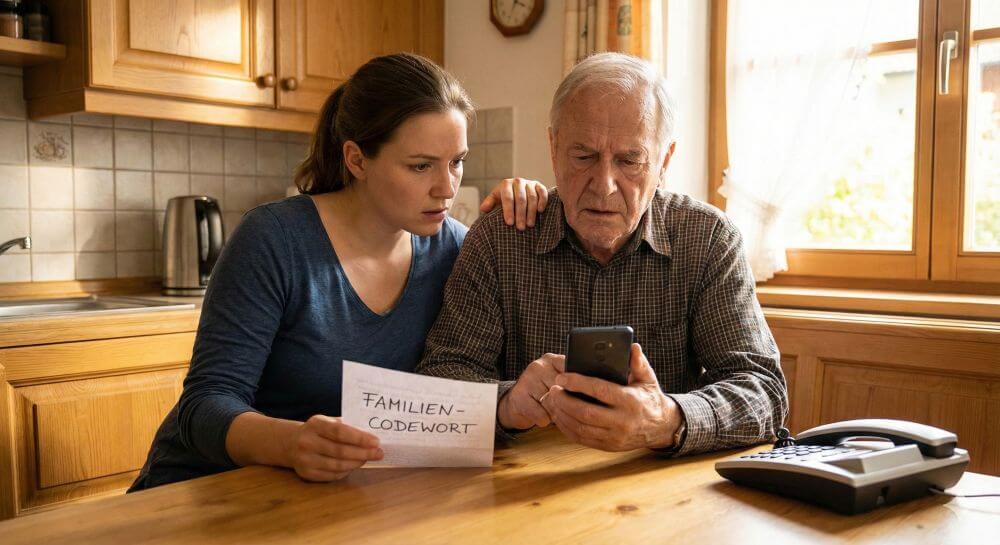
4. Protection against phishing in online banking
4. Protection against phishing in online banking
The methods that scammers are trying to get at your bank details are almost limitless.
In any case, you should pay attention to the following points to make it as difficult as possible for such people:
The methods that scammers are trying to get at your bank details are almost limitless.
In any case, you should pay attention to the following points to make it as difficult as possible for such people:
5. Free checking accounts in comparison
5. Free checking accounts in comparison
6. Installment loans in comparison
6. Installment loans in comparison
Popular Posts:
5 simple security rules against phishing and spam that everyone should know
Deceptively authentic emails from your bank, DHL, or PayPal? That's phishing! Data theft and viruses are a daily threat. We'll show you 5 simple rules (2FA, password managers, etc.) to protect yourself immediately and effectively and help you spot scammers.
The 5 best tips for a clean folder structure on your PC and in the cloud
Say goodbye to file chaos! "Offer_final_v2.docx" is a thing of the past. Learn 5 simple tips for a perfect folder structure on your PC and in the cloud (OneDrive). With proper file naming and archive rules, you'll find everything instantly.
Never do the same thing again: How to record a macro in Excel
Tired of repetitive tasks in Excel? Learn how to create your first personal "magic button" with the macro recorder. Automate formatting and save hours – no programming required! Click here for easy instructions.
IMAP vs. Local Folders: The secret to your Outlook structure and why it matters
Do you know the difference between IMAP and local folders in Outlook? Incorrect use can lead to data loss! We'll explain simply what belongs where, how to clean up your mailbox, and how to archive emails securely and for the long term.
Der ultimative Effizienz-Boost: Wie Excel, Word und Outlook für Sie zusammenarbeiten
Schluss mit manuellem Kopieren! Lernen Sie, wie Sie Excel-Listen, Word-Vorlagen & Outlook verbinden, um personalisierte Serien-E-Mails automatisch zu versenden. Sparen Sie Zeit, vermeiden Sie Fehler und steigern Sie Ihre Effizienz. Hier geht's zur einfachen Anleitung!
Agentic AI: The next quantum leap in artificial intelligence?
Forget simple chatbots! Agentic AI is here: Autonomous AI that plans, learns, and solves complex tasks for you. Discover how AI agents will revolutionize the world of work and your everyday life. Are you ready for the future of artificial intelligence?
Popular Posts:
5 simple security rules against phishing and spam that everyone should know
Deceptively authentic emails from your bank, DHL, or PayPal? That's phishing! Data theft and viruses are a daily threat. We'll show you 5 simple rules (2FA, password managers, etc.) to protect yourself immediately and effectively and help you spot scammers.
The 5 best tips for a clean folder structure on your PC and in the cloud
Say goodbye to file chaos! "Offer_final_v2.docx" is a thing of the past. Learn 5 simple tips for a perfect folder structure on your PC and in the cloud (OneDrive). With proper file naming and archive rules, you'll find everything instantly.
Never do the same thing again: How to record a macro in Excel
Tired of repetitive tasks in Excel? Learn how to create your first personal "magic button" with the macro recorder. Automate formatting and save hours – no programming required! Click here for easy instructions.
IMAP vs. Local Folders: The secret to your Outlook structure and why it matters
Do you know the difference between IMAP and local folders in Outlook? Incorrect use can lead to data loss! We'll explain simply what belongs where, how to clean up your mailbox, and how to archive emails securely and for the long term.
Der ultimative Effizienz-Boost: Wie Excel, Word und Outlook für Sie zusammenarbeiten
Schluss mit manuellem Kopieren! Lernen Sie, wie Sie Excel-Listen, Word-Vorlagen & Outlook verbinden, um personalisierte Serien-E-Mails automatisch zu versenden. Sparen Sie Zeit, vermeiden Sie Fehler und steigern Sie Ihre Effizienz. Hier geht's zur einfachen Anleitung!
Agentic AI: The next quantum leap in artificial intelligence?
Forget simple chatbots! Agentic AI is here: Autonomous AI that plans, learns, and solves complex tasks for you. Discover how AI agents will revolutionize the world of work and your everyday life. Are you ready for the future of artificial intelligence?