The digital arms race:
How AI fuels cyberattacks – and how it protects us from them
The cybersecurity battlefield has fundamentally changed. Where once human hackers painstakingly searched for vulnerabilities, we now stand on the threshold of a new era: the age of algorithmic warfare. Artificial intelligence is no longer just a tool for business or science; it has become the most powerful weapon in the arsenal of cybercriminals—and simultaneously our most important shield.
Welcome to the permanent arms race where AI fights against AI.

Part 1: The Attackers – When AI Becomes a Weapon
Cybercriminals are using AI to make their attacks faster, more sophisticated, and more scalable. The days of clumsy phishing emails with poor grammar are over.
1. Intelligent Spear Phishing and Social Engineering
Classic phishing was a scattershot approach. AI-driven spear phishing is a surgically precise strike. The AI scours massive amounts of data (social media, company websites, public registers) to create highly personalized attacks.
The result: You don’t receive an email from a “Nigerian prince,” but a perfectly worded message from a supposed colleague, referring to a real, recent project and asking you to open the “updated document.” The AI mimics the colleague’s writing style and uses correct internal vocabulary.
2. Deepfakes: The “CEO Fraud 2.0”
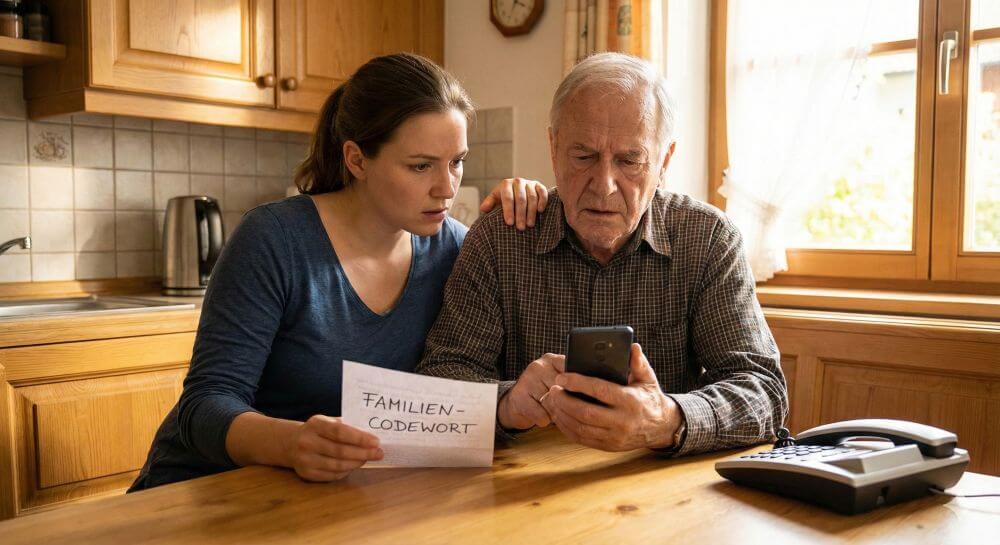
One of the most disturbing developments is the use of audio and video deepfakes. Generative AI can clone a person’s voice with just a few seconds of audio.
The scenario (voice cloning): An employee in the accounting department receives a call. The number is blocked, but the voice is clearly that of the Chief Financial Officer (CFO). The AI voice sounds stressed and explains that an “urgent, confidential emergency payment” to a new supplier must be made immediately. The time pressure and the deceptively realistic voice put the employee under pressure—and the money is gone.
3. Automated Vulnerability Scanning
Instead of a hacker manually scanning a network, they use AI. This algorithm tirelessly tests millions of lines of code, searching for unsecured ports, outdated software, or configuration errors. The AI works 24/7, never tires, and reports an exploitable vulnerability as soon as it’s found—often faster than human IT teams can fix it.
4. Adaptive (Polymorphic) Malware
AI-driven malware isn’t static. It can change its behavior and even its own code once it’s on a network. If it encounters an antivirus program, it analyzes it and tries to modify its signature so it won’t be detected on the next scan.
Part 2: The Defenders – When AI Becomes a Shield
Fortunately, the defense isn’t sleeping. The only realistic answer to AI-driven attacks is an AI-driven defense. Modern security systems no longer rely solely on known “signatures” (like an old antivirus scanner), but on intelligent analysis.
1. User and Entity Behavior Analytics (UEBA)
The defenders’ strongest trump card is User and Entity Behavior Analytics (UEBA). The AI learns the “normal” behavior within a network.
The principle: The AI knows that employee Schmidt from accounting usually logs in between 8 a.m. and 5 p.m., Monday through Friday, and primarily accesses the financial tool.
The anomaly: Suddenly, at 3 a.m. on a Saturday, “employee Schmidt” tries to access the developer servers and download large amounts of data. A traditional antivirus scanner wouldn’t find anything (the password is correct). The AI, however, recognizes this massive behavioral anomaly, immediately raises an alarm, and can automatically lock the account—even before the human administrator receives a call.
2. Automated Response (SOAR)
When an attack occurs at AI speed, the response must happen in milliseconds. SOAR (Security Orchestration, Automation, and Response) platforms use AI to respond to threats without human intervention.
The scenario: The AI behavioral analysis (see above) reports the 3 a.m. anomaly. The SOAR system immediately initiates a predefined playbook:
- Account “Schmidt” is locked.
- The affected device is isolated from the network.
A ticket is created for the IT security team. All of this happens in under a second and prevents the malware from spreading further.
3. Predictive Threat Intelligence
Defense AI analyzes not only the organization’s own network, but also global attack data streams, hacker forums on the dark web, and new malware reports. By recognizing patterns, the AI can predict what kind of attack wave is coming next and recommend that the organization proactively patch certain systems before the attack has even begun.
Conclusion: An arms race without a finish line
We are witnessing an arms race where the speed of innovation determines victory or defeat. AI attacks are too fast and too complex for humans to handle alone.
Yet, despite all the technology, one crucial variable remains: the human element. The most advanced AI defense is useless if an untrained employee falls victim to a deepfake call. Therefore, the combination of AI-powered defense and continuous employee awareness training is the only way forward.
At the same time, the “zero trust” model (never trust, always verify) is becoming the new normal: Every login and every data access must be considered a potential risk and verified—a task that would be impossible without the analytical power of AI.
Beliebte Beiträge
Create a Word letter template with form fields
Create a professional DIN 5008 letter template with form fields and drop-down lists in Microsoft Word, and write letters as easily as you would fill out a form.
Protect Word documents from editing
Protect your documents in Microsoft Word from unauthorized editing or block access completely.
Show and remove duplicate entries in Excel | Tutorial
We explain how to remove duplicate entries from Excel. And also how you can only display duplicate entries in Excel but not delete them immediately in order to decide on a case-by-case basis.
Custom Formatting Excel – Number Format Codes Excel
We use a practical example to explain the importance and possible uses of custom formatting in Excel. Number format codes in Excel are not rocket science!
How to create a dynamic table in Excel
This is how you conveniently create a dynamic table in Excel and have it automatically carry out calculations.
Use macros correctly in Excel
Almost everyone has heard of the term "macro" in the context of Excel, and perhaps has shied away from it because it sounds like a rather complicated affair for which you have to deal with Excel programming.