5 simple security rules against phishing and spam that everyone should know
Every day they land in our inboxes: a supposed package notification from DHL, an urgent payment reminder from an online shop we never ordered from, or an alarming email from our bank urging us to “verify” our account immediately.
These messages are digital decoys. They aim to unsettle us, put us under pressure, and trick us into clicking on something without thinking. The consequences can be devastating: from stolen passwords and emptied bank accounts to computer viruses that encrypt our data.
The good news: You don’t need to be an IT expert to protect yourself effectively. The best firewall is your common sense. We’ll show you five simple but extremely effective security rules for your everyday digital life.

Before we begin, a brief explanation of terms:
Spam: This is the digital version of unwanted mail in your mailbox. Mostly harmless, but annoying advertisements for products or services.
Phishing (pronounced “fishing”): This is digital fraud. Here, the attacker specifically targets your data. The email often looks deceptively genuine (e.g., as if from Amazon, PayPal, or your bank) and tries to trick you into entering your password or credit card information on a fake website.
Malware (malicious software): This is the umbrella term for viruses, Trojans, or ransomware. It is often hidden in email attachments (e.g., in a “.zip” file or a seemingly legitimate Word document).
Now, let’s look at the security measures that will protect you from all of this.
Rule 1: Be paranoid about the sender (healthily suspicious)
The display name in your inbox means nothing. Just because it says “Your Bank e.V.” doesn’t mean the email is genuine. Scammers can enter any name they want as the display name.
The problem: We see the familiar name (e.g., “PayPal”) and our brain switches to trust mode.
The simple solution: Always check the actual email address. In Outlook or on your mobile device, hover your mouse over the name (or tap it) to see the full address.
Practical Example:
Fake: PayPal (service@paypal-sicherheit-123.net)
Genuine: service@paypal.de or service@paypal.com
Rule of thumb: If the domain (the part after the “@” symbol) looks suspicious, contains cryptic numbers, or points to a different country (.ru, .cn), delete the email immediately.
Rule 2: The “mouse hover” trick (Never click blindly!)
Never click on a link or attachment without asking. That’s the golden rule. Attackers hide their traps behind seemingly harmless buttons or text.
The problem: A blue button saying “Confirm account now” or a link like “Track your shipment here” is an invitation to click.
The simple solution: Hover your mouse over the link or button without clicking. Wait a second. The actual destination of the link will be displayed in the bottom corner of your browser or email program (usually the bottom left).
Practical example:
- The text in the link says: www.deutsche-bank.de/login
- The link preview in the bottom left shows: http://login-sicherheit-db.biz/data.php
Result: This is a phishing site!
Exercise particular caution with attachments: Never open unexpected .zip, .exe, .html, or .js files. Be suspicious of Word (.docm) or Excel (.xlsm) files that ask you to “enable macros.” Always ask yourself: Did I expect this file from this sender?
Rule 3: Use a password manager (and strong passwords)
Using the same password for your email account, Amazon, and Facebook login is like using the same key for your front door, your car, and your safe. If one service is hacked, attackers gain access to your entire digital life.
The problem: We can’t remember 20 different, complex passwords ($trOng!_pWd_25?). So we use Mom123 or Summer2024! for everything.
The simple solution: Use a password manager (e.g., Bitwarden, 1Password, KeePass, or the tools integrated into modern browsers).
- You only need to remember one very strong master password.
- The manager creates and stores an extremely complex, unique password for each individual website.
- It automatically fills in these passwords on the actual websites. (Bonus: A good password manager won’t even fill in your Amazon password on a phishing site because it recognizes the URL!)
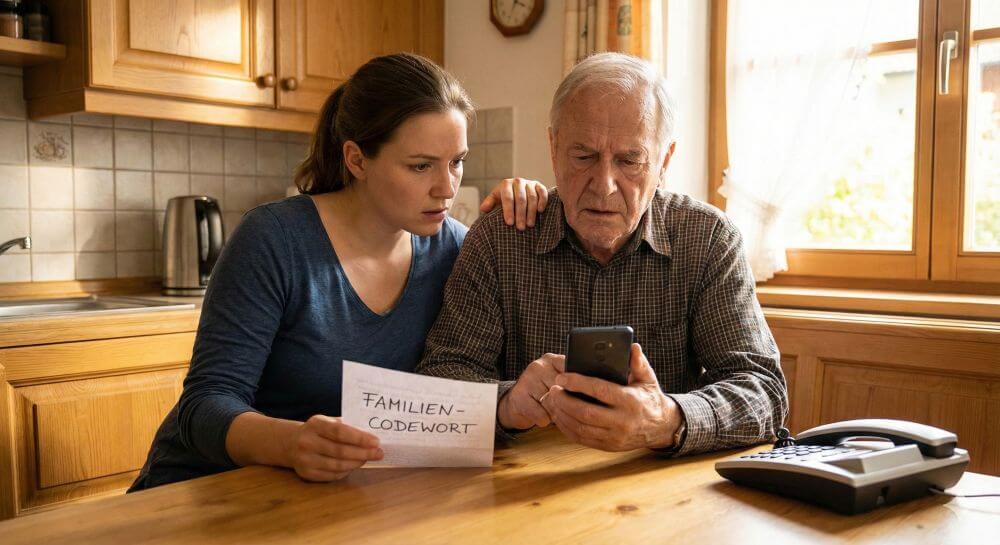
Rule 4: Enable two-factor authentication (2FA)
This is perhaps the single most important security measure you can take today. 2FA is your digital double lock.
The Problem: An attacker has stolen your password (see Rule 3). They can now simply log in on your behalf.
The Simple Solution: Activate 2FA (often called “two-step verification”). When logging in, you’ll then have to provide two things:
- Something you know: Your password.
- Something you have: A one-time code from your mobile phone (via SMS or, even better, via an authenticator app like Google Authenticator or Microsoft Authenticator).
Why it’s so powerful: Even if a hacker steals your password, they can’t log in. They’re standing in front of the double lock, but they’re missing the second key – your mobile phone. Activate this immediately for your most important accounts: email, online banking, Amazon, and all social media.
Rule 5: Keep your software up to date
Updates are annoying, but they’re your computer’s immune system.
The problem: Hackers are constantly finding new security vulnerabilities in Windows, macOS, Outlook, Chrome, and Firefox.
The simple solution: Install updates as soon as they’re available. The best method: Enable automatic updates.
- Outdated software is like an open window on the ground floor of your house. With the update, the developers offer you the chance to close and lock the window. If you ignore the update, you’re practically inviting intruders.
- This applies to your operating system (Windows/Mac), your browser, your office suite, and especially your antivirus program.
Conclusion: Security is a habit, not a product.
You don’t need to be a tech whiz to stay safe. Digital security isn’t a state you buy once, but rather a set of simple, smart habits:
- Check the sender.
- Hover (hold your mouse over) links.
- Use a password manager.
- Enable two-factor authentication (2FA).
- Update your software.
The best firewall is between your ears. Stay skeptical, click thoughtfully, and make it as difficult as possible for attackers.
Beliebte Beiträge
From assistant to agent: Microsoft’s Copilot
Copilot is growing up: Microsoft's AI is no longer an assistant, but a proactive agent. With "Vision," it sees your Windows desktop; in M365, it analyzes data as a "Researcher"; and in GitHub, it autonomously corrects code. The biggest update yet.
Never do the same thing again: How to record a macro in Excel
Tired of repetitive tasks in Excel? Learn how to create your first personal "magic button" with the macro recorder. Automate formatting and save hours – no programming required! Click here for easy instructions.
IMAP vs. Local Folders: The secret to your Outlook structure and why it matters
Do you know the difference between IMAP and local folders in Outlook? Incorrect use can lead to data loss! We'll explain simply what belongs where, how to clean up your mailbox, and how to archive emails securely and for the long term.
Der ultimative Effizienz-Boost: Wie Excel, Word und Outlook für Sie zusammenarbeiten
Schluss mit manuellem Kopieren! Lernen Sie, wie Sie Excel-Listen, Word-Vorlagen & Outlook verbinden, um personalisierte Serien-E-Mails automatisch zu versenden. Sparen Sie Zeit, vermeiden Sie Fehler und steigern Sie Ihre Effizienz. Hier geht's zur einfachen Anleitung!
Microsoft 365 Copilot in practice: Your guide to the new everyday work routine
What can Microsoft 365 Copilot really do? 🤖 We'll show you in a practical way how the AI assistant revolutionizes your daily work in Word, Excel & Teams. From a blank page to a finished presentation in minutes! The ultimate practical guide for the new workday. #Copilot #Microsoft365 #AI
Integrate and use ChatGPT in Excel – is that possible?
ChatGPT is more than just a simple chatbot. Learn how it can revolutionize how you work with Excel by translating formulas, creating VBA macros, and even promising future integration with Office.