Data protection with smartphones is increasingly important
As more and more social processes are carried out with the help of digital technology in modern times, the total amount of personal data today is greater than ever before. However, this development also poses an increased threat to privacy.
For example, mobile devices such as smartphones are susceptible to data misuse.
Data protection with smartphones is increasingly important
As more and more social processes are carried out with the help of digital technology in modern times, the total amount of personal data today is greater than ever before. However, this development also poses an increased threat to privacy.
For example, mobile devices such as smartphones are susceptible to data misuse.
1. Why is privacy becoming more and more relevant?
1. Why is privacy becoming more and more relevant?
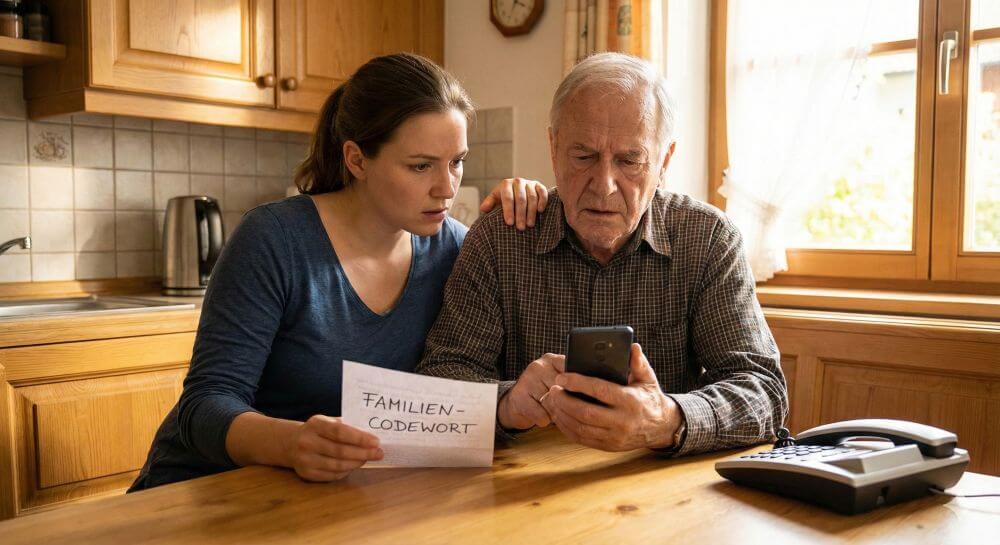
Whether creating personal notes or paying for goods:
In today’s world, most people use their smartphone for a variety of functions. While mobile devices significantly increase their overall comfort in life, they also open up completely new worlds for data collectors. For example, with the help of smartphones, you can quickly create worryingly detailed user profiles.
In addition to companies, more and more hackers are making use of the new possibilities. For example, they steal data with the help of malware and then use it for criminal operations. If you do not want to become a victim of cybercrime or a transparent customer, you should pay close attention to data protection when using your smartphone.
Whether creating personal notes or paying for goods:
In today’s world, most people use their smartphone for a variety of functions. While mobile devices significantly increase their overall comfort in life, they also open up completely new worlds for data collectors. For example, with the help of smartphones, you can quickly create worryingly detailed user profiles.
In addition to companies, more and more hackers are making use of the new possibilities. For example, they steal data with the help of malware and then use it for criminal operations. If you do not want to become a victim of cybercrime or a transparent customer, you should pay close attention to data protection when using your smartphone.
2. For which other devices is data protection important?
2. For which other devices is data protection important?
As a general rule, any device that collects and shares data poses a potential threat to privacy.
Over time, tablets, notebooks and computers accumulate numerous user data that can be used by third parties. Even apparently harmless gadgets such as fitness trackers are not negligible in terms of data protection.
Thus, gadgets of this kind predominantly gather location information, which then reach the smartphone via the Internet in cloud applications of the manufacturer.

Information about your own location, along with contact information, messenger messages, and gallery content, such as photos and videos about the most commonly used data.
As a general rule, any device that collects and shares data poses a potential threat to privacy.
Over time, tablets, notebooks and computers accumulate numerous user data that can be used by third parties. Even apparently harmless gadgets such as fitness trackers are not negligible in terms of data protection.
Thus, gadgets of this kind predominantly gather location information, which then reach the smartphone via the Internet in cloud applications of the manufacturer.

Information about your own location, along with contact information, messenger messages, and gallery content, such as photos and videos about the most commonly used data.
3. How does the data from the smartphone come into the hands of third parties?
3. How does the data from the smartphone come into the hands of third parties?
There are several channels that are used by third parties to collect user data.
Many data collectors use applications such as apps or games to obtain information. Experience has shown that the majority of consumers pay little attention to rights clearance during installation.
It is not uncommon for apps to require access to sensitive areas such as contact information, even though they are unrelated to the feature.
Another channel is the use of hidden malicious software. Especially with apps from unknown sources that need to be installed separately, the risk of Trojans and similar programs is very high.
There are several channels that are used by third parties to collect user data.
Many data collectors use applications such as apps or games to obtain information. Experience has shown that the majority of consumers pay little attention to rights clearance during installation.
It is not uncommon for apps to require access to sensitive areas such as contact information, even though they are unrelated to the feature.
Another channel is the use of hidden malicious software. Especially with apps from unknown sources that need to be installed separately, the risk of Trojans and similar programs is very high.
4. How can users protect themselves against data misuse?
4. How can users protect themselves against data misuse?
Similar to when calling abroad, for example, users must be extremely cautious about installing apps.
In any case, only applications from trusted sources such as the official app stores should be downloaded. Furthermore, attention must be paid to the rights release with each installation. For example, if a flashlight app requires access to the phone book, that does not exactly mean the seriousness of the application.
To prevent unauthorized access to the location data, it is advisable to turn on the GPS function only when actively used.

It should also be noted that pictures taken with a smartphone usually contain location information in the form of metadata. If you want to play it safe, you should remove it with an image editor.
Since a modern smartphone is similar in principle to a computer, the operating system should be adequately protected. Here it is particularly important that the software is regularly updated by updates.
In addition, it makes sense to additionally install a separate antivirus program. To minimize the data stream, security settings should also be enabled in installed apps.
For example, pop-ups and cookies can be specifically controlled in the browser. The browsing history should also be deleted regularly in the course of data protection.
Similar to when calling abroad, for example, users must be extremely cautious about installing apps.
In any case, only applications from trusted sources such as the official app stores should be downloaded. Furthermore, attention must be paid to the rights release with each installation. For example, if a flashlight app requires access to the phone book, that does not exactly mean the seriousness of the application.
To prevent unauthorized access to the location data, it is advisable to turn on the GPS function only when actively used.

It should also be noted that pictures taken with a smartphone usually contain location information in the form of metadata. If you want to play it safe, you should remove it with an image editor.
Since a modern smartphone is similar in principle to a computer, the operating system should be adequately protected. Here it is particularly important that the software is regularly updated by updates.
In addition, it makes sense to additionally install a separate antivirus program. To minimize the data stream, security settings should also be enabled in installed apps.
For example, pop-ups and cookies can be specifically controlled in the browser. The browsing history should also be deleted regularly in the course of data protection.
About the author:
About the author:
Popular Posts:
Die Renaissance des Büros: Warum Präsenz manchmal unschlagbar ist
Homeoffice bietet Fokus, doch das Büro bleibt als sozialer Anker unverzichtbar. Spontane Innovation, direktes Voneinander-Lernen und echtes Wir-Gefühl sind digital kaum zu ersetzen. Lesen Sie, warum Präsenz oft besser ist und wie die ideale Mischung für moderne Teams aussieht.
New Work & Moderne Karriere: Warum die Karriereleiter ausgedient hat
Die klassische Karriereleiter hat ausgedient. New Work fordert ein neues Denken: Skills statt Titel, Netzwerk statt Hierarchie. Erfahre, warum das "Karriere-Klettergerüst" deine neue Realität ist und wie du dich mit 4 konkreten Schritten zukunftssicher aufstellst.
Die Homeoffice-Falle: Warum unsichtbare Arbeit deine Beförderung gefährdet
Produktiv im Homeoffice, doch befördert wird der Kollege im Büro? Willkommen in der Homeoffice-Falle. "Proximity Bias" lässt deine Leistung oft unsichtbar werden. Lerne 4 Strategien, wie du auch remote sichtbar bleibst und deine Karriere sicherst – ganz ohne Wichtigtuerei.
Microsoft Loop in Teams: The revolution of your notes?
What exactly are these Loop components in Microsoft Teams? We'll show you how these "living mini-documents" can accelerate your teamwork. From dynamic agendas to shared, real-time checklists – discover practical use cases for your everyday work.
Career booster 2026: These Microsoft Office skills will take you further!
A new year, new career opportunities! But which Office skills will really be in demand in 2026? "Skilled use" is no longer enough. We'll show you today's must-haves – like advanced Excel, using AI in the office, and relevant certifications for your resume.
Why Zero Trust doesn’t work without identity protection!
Zero Trust means: Trust no one, verify everyone. Identity protection is at the heart of this modern security model. Learn how IAM, MFA, Conditional Access, and the principle of least privilege effectively protect your business when the old network perimeter is gone.
Popular Posts:
Die Renaissance des Büros: Warum Präsenz manchmal unschlagbar ist
Homeoffice bietet Fokus, doch das Büro bleibt als sozialer Anker unverzichtbar. Spontane Innovation, direktes Voneinander-Lernen und echtes Wir-Gefühl sind digital kaum zu ersetzen. Lesen Sie, warum Präsenz oft besser ist und wie die ideale Mischung für moderne Teams aussieht.
New Work & Moderne Karriere: Warum die Karriereleiter ausgedient hat
Die klassische Karriereleiter hat ausgedient. New Work fordert ein neues Denken: Skills statt Titel, Netzwerk statt Hierarchie. Erfahre, warum das "Karriere-Klettergerüst" deine neue Realität ist und wie du dich mit 4 konkreten Schritten zukunftssicher aufstellst.
Die Homeoffice-Falle: Warum unsichtbare Arbeit deine Beförderung gefährdet
Produktiv im Homeoffice, doch befördert wird der Kollege im Büro? Willkommen in der Homeoffice-Falle. "Proximity Bias" lässt deine Leistung oft unsichtbar werden. Lerne 4 Strategien, wie du auch remote sichtbar bleibst und deine Karriere sicherst – ganz ohne Wichtigtuerei.
Microsoft Loop in Teams: The revolution of your notes?
What exactly are these Loop components in Microsoft Teams? We'll show you how these "living mini-documents" can accelerate your teamwork. From dynamic agendas to shared, real-time checklists – discover practical use cases for your everyday work.
Career booster 2026: These Microsoft Office skills will take you further!
A new year, new career opportunities! But which Office skills will really be in demand in 2026? "Skilled use" is no longer enough. We'll show you today's must-haves – like advanced Excel, using AI in the office, and relevant certifications for your resume.
Why Zero Trust doesn’t work without identity protection!
Zero Trust means: Trust no one, verify everyone. Identity protection is at the heart of this modern security model. Learn how IAM, MFA, Conditional Access, and the principle of least privilege effectively protect your business when the old network perimeter is gone.