How to create secure passwords
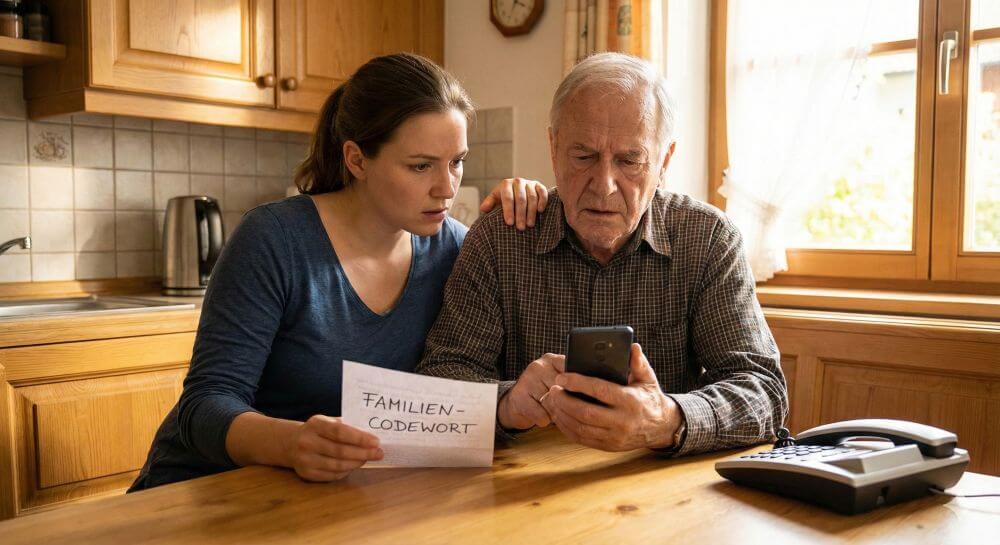
The number of online accounts that everyone in the meantime has in tow is steadily increasing. These include social media accounts, e-mail accounts, and countless access to online shops. Many, however, always use one and the same password for the various accesses, which makes it easy for hackers – once the password has been breached – to make some nonsense with their access data in no time at all.
According to Statista data, only very few Germans use a sufficient number of different passwords.
This may be due to the fact that many are not aware of the importance of password security, and on the other hand, of course, because it seems almost impossible to remember so many different passwords that should ideally be as complex as possible.
How to create secure passwords
The number of online accounts that everyone in the meantime has in tow is steadily increasing. These include social media accounts, e-mail accounts, and countless access to online shops. Many, however, always use one and the same password for the various accesses, which makes it easy for hackers – once the password has been breached – to make some nonsense with their access data in no time at all.
According to Statista data, only very few Germans use a sufficient number of different passwords.
This may be due to the fact that many are not aware of the importance of password security, and on the other hand, of course, because it seems almost impossible to remember so many different passwords that should ideally be as complex as possible.
The length of the password is important
When assigning a password, you are often asked to use at least one uppercase letter and a special character like % or /. However, what is not sufficiently checked is that the password is long enough. Although there is a minimum number of characters required, this is often too short, according to the National Institute of Standards and Technology (NIST).
Because a password should be at least 8 characters. And this is really only the absolute minimum! Better are 12 or 16 characters. It would also be desirable to allow the providers spaces in passwords, which would increase the possibilities of complexity, and thus the security again.
A short password with, for example, only 8 characters, even if you spam them with special characters, can be detected in a relatively short time by computers that do nothing but try out passwords. And already the culprits have gotten a hit again to drive Schindluder with your data. If the same password applies to other accounts then the damage can be considerable.
For if you buy at your expense on the Internet, and the goods are delivered to any packing stations you may not notice this at first, or very late. Then it will be difficult if not impossible to find the perpetrators who often sit abroad, while you stay at high cost. Because it was not hacked the portal where your access data were tapped, but you yourself were the victim of a hacker attack, which you have apparently made possible by insufficient security arrangements.
The length of the password is important
When assigning a password, you are often asked to use at least one uppercase letter and a special character like % or /. However, what is not sufficiently checked is that the password is long enough. Although there is a minimum number of characters required, this is often too short, according to the National Institute of Standards and Technology (NIST).
Because a password should be at least 8 characters. And this is really only the absolute minimum! Better are 12 or 16 characters. It would also be desirable to allow the providers spaces in passwords, which would increase the possibilities of complexity, and thus the security again.
A short password with, for example, only 8 characters, even if you spam them with special characters, can be detected in a relatively short time by computers that do nothing but try out passwords. And already the culprits have gotten a hit again to drive Schindluder with your data. If the same password applies to other accounts then the damage can be considerable.
For if you buy at your expense on the Internet, and the goods are delivered to any packing stations you may not notice this at first, or very late. Then it will be difficult if not impossible to find the perpetrators who often sit abroad, while you stay at high cost. Because it was not hacked the portal where your access data were tapped, but you yourself were the victim of a hacker attack, which you have apparently made possible by insufficient security arrangements.
How do I remember long passwords?
As we said before, with strong passwords, the creativity and convenience of many users are failing to come up with a sensible password. Many then resort to password generators, which are however not particularly recommendable, because here the passwords created at some point are the same, and can easily be spied out.
Another option is to use a password manager for all your passwords. Here then a single master password is sufficient to get to all other data. But the BSI has come to the conclusion that this alternative is risky. Because if only a single password is needed to then get sorted by a variety of passwords with the associated portals that may not be the right solution.
Your passwords should be as individual as possible, and preferably consist of a whole sentence, in which you then exchange certain letters for numbers (for example, an E against a 3, or a B against an 8, etc.). The sentence should also be really individual and not something like “youcannot getinhere”.
It is best to form sentences that have emerged from personal life events that really only you and maybe a handful of people from your personal environment can know, and convert them by exchanging letters for numbers and / or special characters, and uppercase and lowercase letters ,
So take the time to invest in your online security, because the damage caused by inadequate security measures can bring you much more trouble.
How do I remember long passwords?
As we said before, with strong passwords, the creativity and convenience of many users are failing to come up with a sensible password. Many then resort to password generators, which are however not particularly recommendable, because here the passwords created at some point are the same, and can easily be spied out.
Another option is to use a password manager for all your passwords. Here then a single master password is sufficient to get to all other data. But the BSI has come to the conclusion that this alternative is risky. Because if only a single password is needed to then get sorted by a variety of passwords with the associated portals that may not be the right solution.
Your passwords should be as individual as possible, and preferably consist of a whole sentence, in which you then exchange certain letters for numbers (for example, an E against a 3, or a B against an 8, etc.). The sentence should also be really individual and not something like “youcannot getinhere”.
It is best to form sentences that have emerged from personal life events that really only you and maybe a handful of people from your personal environment can know, and convert them by exchanging letters for numbers and / or special characters, and uppercase and lowercase letters ,
So take the time to invest in your online security, because the damage caused by inadequate security measures can bring you much more trouble.
Popular Posts:
Ad-free home network: Install Pi-hole on Windows
Say goodbye to ads on smart TVs and in apps: Pi-hole software turns your Windows laptop into a network filter. This article explains step-by-step how to install it via Docker and configure the necessary DNS settings in your FRITZ!Box.
How to tune your FRITZ!Box into a professional call server
A professional telephone system can be built using a FRITZ!Box and a laptop. This article shows step by step how to use the free software "Phoner" to schedule announcements and record calls – including important legal information (§ 201 StGB).
Why to-do lists are a waste of time
Do you feel unproductive at the end of the day, even though you've worked hard? Your to-do list is to blame. It tempts you to focus on easy tasks and ignores your limited time. This article explains why lists are "self-deception" and why professionals use a calendar instead.
Smartphone Wi-Fi security: Public hotspots vs. home network
Is smartphone Wi-Fi a security risk? This article analyzes in detail threats such as evil twin attacks and explains protective measures for when you're on the go. We also clarify why home Wi-Fi is usually secure and how you can effectively separate your smart home from sensitive data using a guest network.
Warum dein Excel-Kurs Zeitverschwendung ist – was du wirklich lernen solltest!
Hand aufs Herz: Wann hast du zuletzt eine komplexe Excel-Formel ohne Googeln getippt? Eben. KI schreibt heute den Code für dich. Erfahre, warum klassische Excel-Trainings veraltet sind und welche 3 modernen Skills deinen Marktwert im Büro jetzt massiv steigern.
Cybersicherheit: Die 3 größten Fehler, die 90% aller Mitarbeiter machen
Hacker brauchen keine Codes, sie brauchen nur einen unaufmerksamen Mitarbeiter. Von Passwort-Recycling bis zum gefährlichen Klick: Wir zeigen die drei häufigsten Fehler im Büroalltag und geben praktische Tipps, wie Sie zur menschlichen Firewall werden.
Popular Posts:
Ad-free home network: Install Pi-hole on Windows
Say goodbye to ads on smart TVs and in apps: Pi-hole software turns your Windows laptop into a network filter. This article explains step-by-step how to install it via Docker and configure the necessary DNS settings in your FRITZ!Box.
How to tune your FRITZ!Box into a professional call server
A professional telephone system can be built using a FRITZ!Box and a laptop. This article shows step by step how to use the free software "Phoner" to schedule announcements and record calls – including important legal information (§ 201 StGB).
Why to-do lists are a waste of time
Do you feel unproductive at the end of the day, even though you've worked hard? Your to-do list is to blame. It tempts you to focus on easy tasks and ignores your limited time. This article explains why lists are "self-deception" and why professionals use a calendar instead.
Smartphone Wi-Fi security: Public hotspots vs. home network
Is smartphone Wi-Fi a security risk? This article analyzes in detail threats such as evil twin attacks and explains protective measures for when you're on the go. We also clarify why home Wi-Fi is usually secure and how you can effectively separate your smart home from sensitive data using a guest network.
Warum dein Excel-Kurs Zeitverschwendung ist – was du wirklich lernen solltest!
Hand aufs Herz: Wann hast du zuletzt eine komplexe Excel-Formel ohne Googeln getippt? Eben. KI schreibt heute den Code für dich. Erfahre, warum klassische Excel-Trainings veraltet sind und welche 3 modernen Skills deinen Marktwert im Büro jetzt massiv steigern.
Cybersicherheit: Die 3 größten Fehler, die 90% aller Mitarbeiter machen
Hacker brauchen keine Codes, sie brauchen nur einen unaufmerksamen Mitarbeiter. Von Passwort-Recycling bis zum gefährlichen Klick: Wir zeigen die drei häufigsten Fehler im Büroalltag und geben praktische Tipps, wie Sie zur menschlichen Firewall werden.