Safe at Home: The Ultimate Guide to Your PC and Your Wi-Fi
Our home is our safe haven – and that’s no longer just true for the physical world. With working from home, online banking, streaming services, and a growing array of smart devices, our home network has become the digital heart of our lives. But how well protected is this digital fortress really?
Many people neglect the security of their personal devices and networks because the topic seems complex and intimidating. The good news is that with a few basic, easy-to-understand steps, you can significantly increase the security of your PC and Wi-Fi network. In this guide, we’ll walk you through the most important best practices in a clear and concise way.

Part 1: The Foundation – How to Secure Your Wi-Fi Network
Your Wi-Fi router is the gateway to your digital home. If this gateway is unsecured, all the doors behind it are open. So let’s start with the most important component.
1. Change the Default Router Password
Every router comes with a default administrator password (often “admin,” “password,” or found on a sticker). This password doesn’t protect your Wi-Fi network, but rather access to the router’s configuration interface. Hackers are familiar with these default passwords.
Your Task: Log in to your router’s user interface (the address is usually 192.168.1.1 or 192.168.0.1) and change the administrator password to a unique, strong password.
2. Use the strongest encryption: WPA3
Wi-Fi encryption ensures that no one can eavesdrop on your data. The current gold standard is WPA3. Older devices may only support WPA2, which is still considered secure. You should avoid outdated standards like WEP or WPA under all circumstances.
Your task: Check in your router settings that WPA3 or WPA2 is enabled as the encryption method.
3. Choose a strong and unique Wi-Fi password
The Wi-Fi password (also called network key) is the key you and your guests use to connect. “FamilyMeier123” is not a secure password.
Best Practice:
- At least 12-15 characters long.
- A mix of uppercase and lowercase letters, numbers, and special characters.
Tip: Create an easy-to-remember sentence and modify it. “I drink two cups of coffee every morning!” becomes ItjM2Tk!.
4. Set up a guest Wi-Fi network
Your friends and visitors want to use the internet? Perfect! But do they need access to your entire home network, including your laptop or network drive? No. Almost every modern router offers the option of creating a separate guest network.
The advantage: Guests can browse the internet but are completely isolated from your private network and your devices.
Your task: Activate the guest network function on your router and give it its own separate password.
5. Keep your router firmware up to date
Your router’s software (firmware) is regularly updated by the manufacturer to close security gaps. Outdated firmware poses a huge security risk.
Your task: If possible, activate the automatic update function in your router settings. Otherwise, manually check the manufacturer’s website for updates at least every few months.
Part 2: The Guardians – How to harden your computer
A secure network is half the battle. The other half is a well-protected computer.
1. Operating System and Software: Always Up-to-Date
First things first: Updates aren’t a nuisance, but your most important line of defense. They close known security gaps that attackers would otherwise exploit.
Your task: Enable automatic updates for your operating system (Windows, macOS) and important programs such as your web browser (Chrome, Firefox, Edge) and your office suite. Always perform updates promptly when prompted.
2. Antivirus and Firewall: The Digital Alarm System
Modern operating systems already have excellent security tools built in. Windows Defender is a fully-fledged and reliable antivirus solution. The integrated Windows Firewall blocks unwanted network access.
Your task: Ensure that both the antivirus program’s real-time protection and the firewall are enabled. For most home users, no additional third-party software is necessary.
3. Backups: Your Lifeline in an Emergency
The 3-2-1 Backup Rule:
- 3 copies of your data (the original plus two backups).
- 2 different storage media (e.g., your PC and an external hard drive).
- 1 copy off-site (e.g., in cloud storage like OneDrive or with a family member).
Your task: Set up regular, automatic data backups to an external hard drive and/or the cloud. Windows offers the “File History” feature for this purpose.
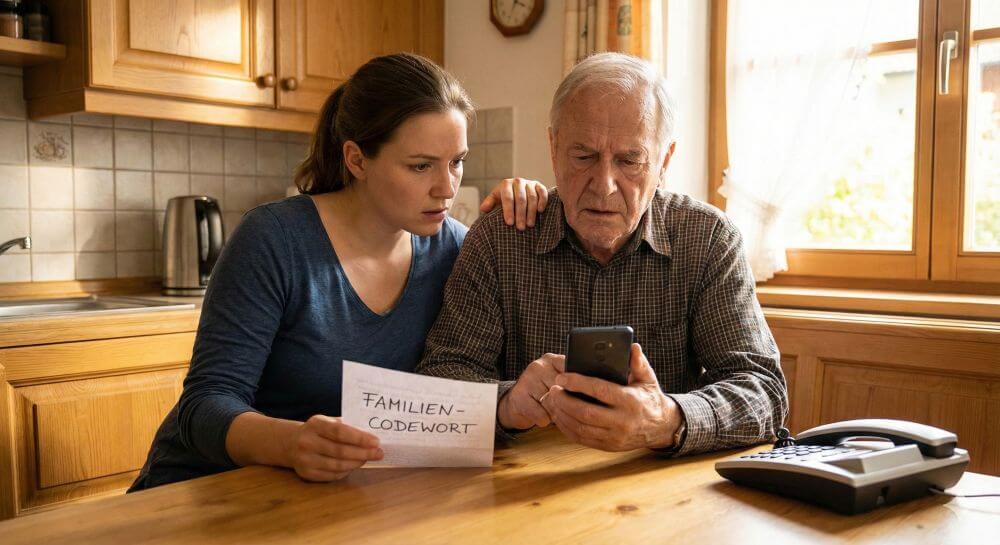
Part 3: The weakest link – The person in front of the screen
The best technology is useless if you open the door to attackers yourself. Healthy skepticism and safe behavior are essential.
1. Recognizing Phishing Emails
Phishing is the attempt to trick you into clicking on a malicious link and revealing your passwords using fake emails (e.g., from your bank, Amazon, or PayPal).
Warning Signs:
- Urgent Action Required: “Your account will be locked if you don’t act immediately!”
- Impersonal Salutation: “Dear Customer” instead of your name.
- Spelling and Grammar Mistakes.
- Suspicious Sender: Hover your mouse over the sender’s name to see the real email address.
Links That Don’t Match the Destination: Hover your mouse over a link to see the actual web address before clicking.
2. Strong Passwords and Two-Factor Authentication (2FA)
Never use the same password for multiple important services. If one service is hacked, all your accounts are at risk. A password manager (e.g., Bitwarden, 1Password) helps you create and securely store a unique, strong password for each service.
Additionally, enable two-factor authentication (2FA) wherever possible. This requires a second factor (e.g., a code from an app on your phone) in addition to your password to log in. Even if someone steals your password, they cannot access your account without your phone.
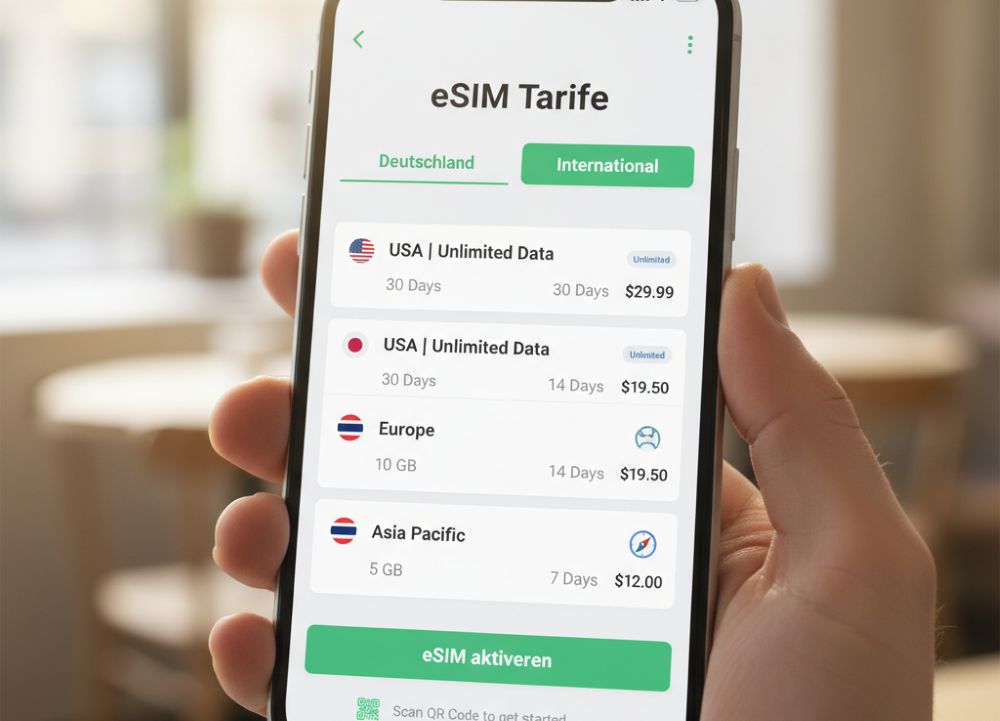
3. Caution on Public Wi-Fi Networks
Open Wi-Fi in cafes, hotels, or airports is convenient but insecure. Avoid logging into sensitive services like online banking or transmitting confidential data on public networks. If it’s unavoidable, use a VPN (Virtual Private Network) to encrypt your connection.
Conclusion: Security is not a state, but a process.
Digital security might seem like a huge amount of work at first glance. But as you can see, it’s many small but effective steps that make all the difference. Take an hour to go through these points. Make security a regular habit – like locking your front door. Your digital self will thank you.
Beliebte Beiträge
Microsoft Office 2021 – Is the switch worth it?
Since October 5, 2021, the time has finally come. After Office 2019, Office 2021 is now at the start. We took a closer look at the new Office version and found out whether the switch is worth it.
Excel Scenario manager and target value search
How you can use the scenario manager and target value search in Excel 2016/2019 to present complex issues in a space-saving and clear way.
Insert controls and form fields in Word
With Microsoft Word you can not only comfortably create letters, lists and articles with tables of contents, but also go one step further, and Set up your own forms using controls.
Apply nested functions in Excel
Nested functions in Excel offer the possibility to combine several arguments with each other or to exclude conditions. We explain how it works.
Office 2021 – Everything you need to know about price, versions and scope
Shortly before the release, Microsoft announced the prices and scope for the new Office 2021. We are a little amazed at what is coming.
Insert Excel spreadsheets into Word Documents
So you can easily insert Excel spreadsheets into Word and link them together to get a dynamic document.