More than just a password:
Why 2-factor authentication is mandatory today
We all know the mantra: Use a long, complex password, and a different one for every service. In theory, that’s good advice. In practice, however, it’s incomplete. A password alone—no matter how strong—is no longer sufficient protection for your valuable digital accounts.
The reality is: Your passwords are probably already circulating. Massive data leaks at large companies (like LinkedIn, Adobe, and countless others) have resulted in billions of email-password combinations being traded on the dark web.
This is where two-factor authentication (2FA) comes in. It’s no longer an optional extra, but a fundamental necessity for anyone who uses the internet seriously.

What exactly is two-factor authentication?
Two-factor authentication (2FA) is an additional layer of security for your online accounts. Instead of logging in with just one factor (your password), you need a second, independent factor to prove your identity.
Authentication is based on three possible factor types:
- Knowledge (Something you know): The classic password or PIN.
- Possession (Something you possess): A physical object, usually your smartphone (for an app or SMS) or a special USB security key.
- Inherence (Something you are): Biometric characteristics such as your fingerprint, facial scan (e.g., Face ID), or iris scan.
Two-factor authentication always requires a combination of two of these different types. (Entering two passwords consecutively would not be 2FA, as it uses the same “knowledge” factor.)
How does 2FA work in practice?
- The most common scenario combines knowledge and possession:
- You visit a website (e.g., your email inbox or PayPal) and enter your username and password (Factor 1: Knowledge).
- Instead of logging you in directly, the website now prompts you for a second step (Factor 2: Possession).
- You now have to enter a code that is generated only at this moment and only for you.
There are common methods for this second factor:
- Authenticator apps (Very secure): Apps like Google Authenticator, Microsoft Authenticator, or Authy generate a new, 6-digit one-time code on your smartphone every 30 seconds. This is the recommended standard method.
- SMS Codes (Secure): The service sends you the code via SMS. This is more convenient but more vulnerable to fraud (e.g., “SIM swapping,” where criminals hijack your mobile phone number).
- Hardware Keys (Most Secure): A small USB stick (e.g., a YubiKey) that you have to plug in and/or touch. This is the gold standard and even protects against sophisticated phishing sites.
Why 2FA is indispensable (“mandatory”) today
The explanation for why 2FA is so essential boils down to one core problem: A password is only secure until it’s stolen—and that happens constantly.
Here are the reasons why a password alone is no longer sufficient:
1. The Flood of Data Breaches
You can have the strongest password in the world. If the service you use it for gets hacked, your password is in the hands of criminals. It’s not a question of “if,” but “when.” Hackers collect these stolen lists.
2. The “Credential Stuffing” Tactic
Hackers take these billions of stolen email-password combinations and automatically try them on all other services (e.g., Amazon, PayPal, Netflix, banks). Since so many people reuse passwords, the success rate for attackers is extremely high.
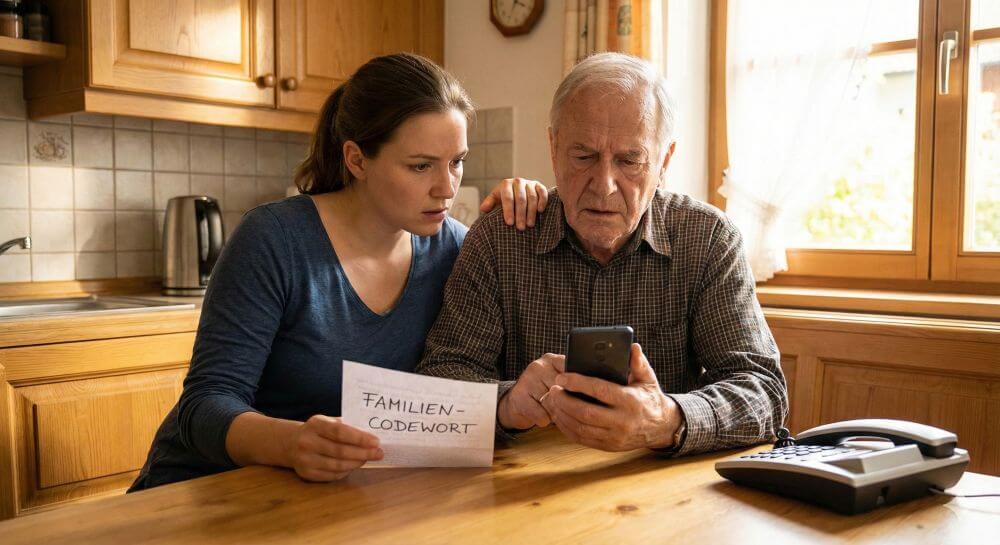
3. The Rise of Phishing
Phishing emails are becoming increasingly sophisticated. They lure you to fake login pages that look exactly like the original. You enter your password and thereby transmit it directly to the fraudsters.
- 2FA is the firewall
Here the value of 2FA becomes obvious:
- Even if a hacker has your password – whether through a data breach or phishing – they cannot log in.
- As soon as the attacker enters your stolen password on the legitimate website, they are asked for the second factor. They don’t have this code because they don’t have access to your smartphone or hardware key. The attack fails at this second barrier.
The stakes have become too high
Previously, a password might have protected access to a forum. Today, it protects your entire digital life:
- Finances: Your bank account, PayPal, cryptocurrency exchanges.
- Identity: Your primary email account (the “master key” to all your other accounts), your cloud storage (containing private photos and documents), your social media accounts.
Losing access to your primary email account is catastrophic. An attacker can use it to reset the passwords for all your other services and completely take over your digital identity.
Conclusion: From “nice-to-have” to “must-have”
Setting up 2FA often takes just two minutes. Those two minutes are the best investment you can make in your digital security.
Yes, it’s a tiny extra step when logging in on a new device. But that small effort is nothing compared to the nightmare of having to recover a compromised bank account or a stolen identity.
Don’t think of 2FA as a nuisance, but rather as what it is in 2024: an essential digital lock. Review the settings of your most important accounts (email, banking, social media) and enable 2FA everywhere.
Conclusion
The “Your PayPal account has been restricted” scam is a classic phishing attack that preys on users’ fears. The best protection is healthy skepticism. Don’t trust any email that urges you to take immediate action, and if in doubt, always log into your account manually via the official website.
Beliebte Beiträge
Microsoft Office 2021 – Is the switch worth it?
Since October 5, 2021, the time has finally come. After Office 2019, Office 2021 is now at the start. We took a closer look at the new Office version and found out whether the switch is worth it.
Excel Scenario manager and target value search
How you can use the scenario manager and target value search in Excel 2016/2019 to present complex issues in a space-saving and clear way.
Insert controls and form fields in Word
With Microsoft Word you can not only comfortably create letters, lists and articles with tables of contents, but also go one step further, and Set up your own forms using controls.
Apply nested functions in Excel
Nested functions in Excel offer the possibility to combine several arguments with each other or to exclude conditions. We explain how it works.
Office 2021 – Everything you need to know about price, versions and scope
Shortly before the release, Microsoft announced the prices and scope for the new Office 2021. We are a little amazed at what is coming.
Insert Excel spreadsheets into Word Documents
So you can easily insert Excel spreadsheets into Word and link them together to get a dynamic document.